
Cybersecurity Houston: Accounts Payable Teams Need to Stop AI-Enhanced Fraud
Reviewing Payment Workflows For Impersonation Risk – The Fix Is Process, Not Stronger Instincts
AI tools have made business email compromise faster, more convincing, and harder to spot. Here's what Houston finance teams need to defend against the new wave of accounts payable scams.
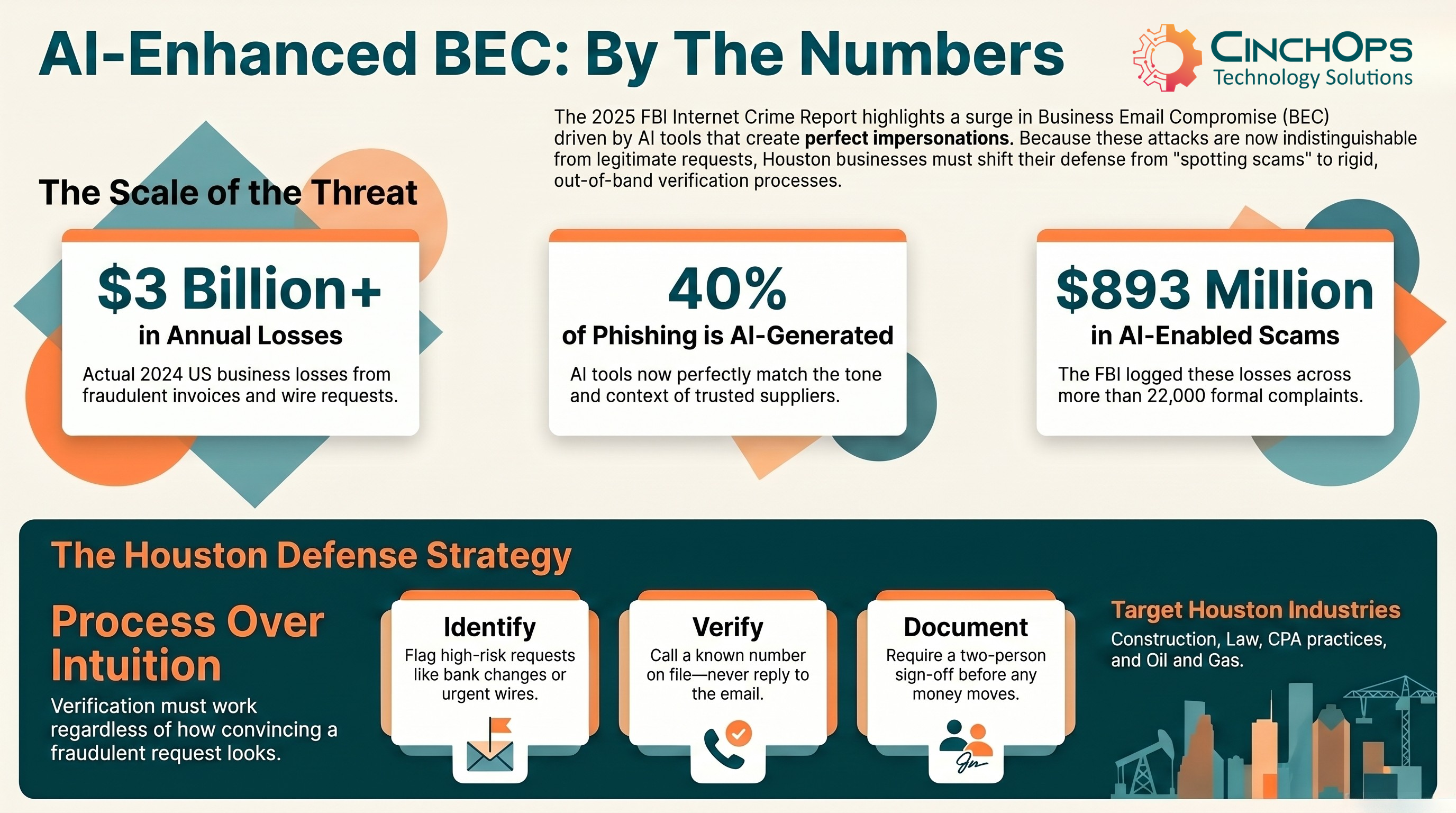
Business email compromise cost US companies more than $3 billion in 2024 according to the FBI's 2025 Internet Crime Report. That figure is not a forecast or a worst-case projection. It is one year of money that walked out the door of small and mid-sized businesses, often through a single fraudulent invoice or wire request that looked legitimate enough to pay.
The cybersecurity Houston accounts payable teams need today is different from what worked even two years ago. AI tools have removed the awkward grammar, mismatched logos, and clumsy phrasing that gave older phishing emails away. The new generation of BEC attacks is grammatically clean, contextually aware, and increasingly delivered by voice as well as email. Houston, Katy, and Sugar Land finance teams are seeing it.
CinchOps is a managed IT services provider based in Katy, Texas, serving small and mid-sized businesses with 10 to 200 employees across the Houston metro area. CinchOps specializes in cybersecurity, managed IT support, network security, VoIP, and SD-WAN, with deep experience defending finance, law firms, CPA practices, and construction back-office teams from impersonation fraud.
Why AP Teams Sit in the Crosshairs
Accounts payable lives at the intersection of trust and timing. AP teams process invoices, manage supplier records, and execute payments under pressure to keep operations moving. For attackers, that combination is ideal. Most successful fraud doesn't involve breaking into systems. It involves convincing the right person to send money to the wrong account.
The FBI's Internet Crime Complaint Center has consistently found that BEC attacks rely on impersonation. Posing as a trusted executive, supplier, or internal colleague to redirect payments or update bank details before anyone notices. AI has made that impersonation dramatically more scalable. What once took skill and time to craft now happens at machine speed across hundreds of targets at once.
"Fraud doesn't break in. It walks in through the front door wearing the right uniform. The job of cybersecurity isn't to make your team paranoid. It's to make sure no single email, no single phone call, can move money on its own."
What AI-Enhanced Fraud Looks Like in Practice
Emails That Blend Into Normal Workflow. Traditional phishing relied on volume and imperfection. AI changed that. Modern BEC emails are grammatically correct and written in the specific tone of the executive or supplier being impersonated. They reference active projects, current invoice numbers, and upcoming payment runs. For a team processing high volumes of routine correspondence, that level of familiarity is exactly what lowers the guard.
Invoice And Payment Redirection. One of the most common AP fraud patterns is payment redirection. Attackers intercept a legitimate invoice exchange and quietly alter the destination account. Then they send a short message claiming a supplier has updated its banking details, or re-issue a real invoice with minor modifications. The surrounding content looks legitimate because, in many cases, it is. The attacker is replaying real correspondence with one field changed.
Voice Cloning And Executive Impersonation. Email isn't the only channel. AI voice-cloning tools can replicate a person's voice from a short audio sample, which makes it possible to leave convincing voicemails or place calls that sound like a known executive. For AP teams accustomed to verbal approvals on high-value or urgent payments, this removes one of the few remaining verification methods that email security tools can't address on their own.
Here's how this typically plays out: a Houston-area construction firm receives an emailed invoice for the same supplier they've used for 18 months. The invoice references the right job site, the right PO number, and the right amount. Only the bank account has changed. A follow-up voicemail from "the supplier" confirms the update. Without out-of-band verification, that payment goes out and isn't recoverable.
Why Traditional Checks No Longer Work
Security awareness training still matters, and investing in it is still worthwhile. But AI has changed what AP teams are up against. Attacks no longer carry the signals that older training programs focused on: awkward phrasing, mismatched logos, odd sender addresses, generic greetings. Modern fraud emails reference the recipient's organization, their active suppliers, and current invoice values pulled from public sources or earlier intercepted messages.
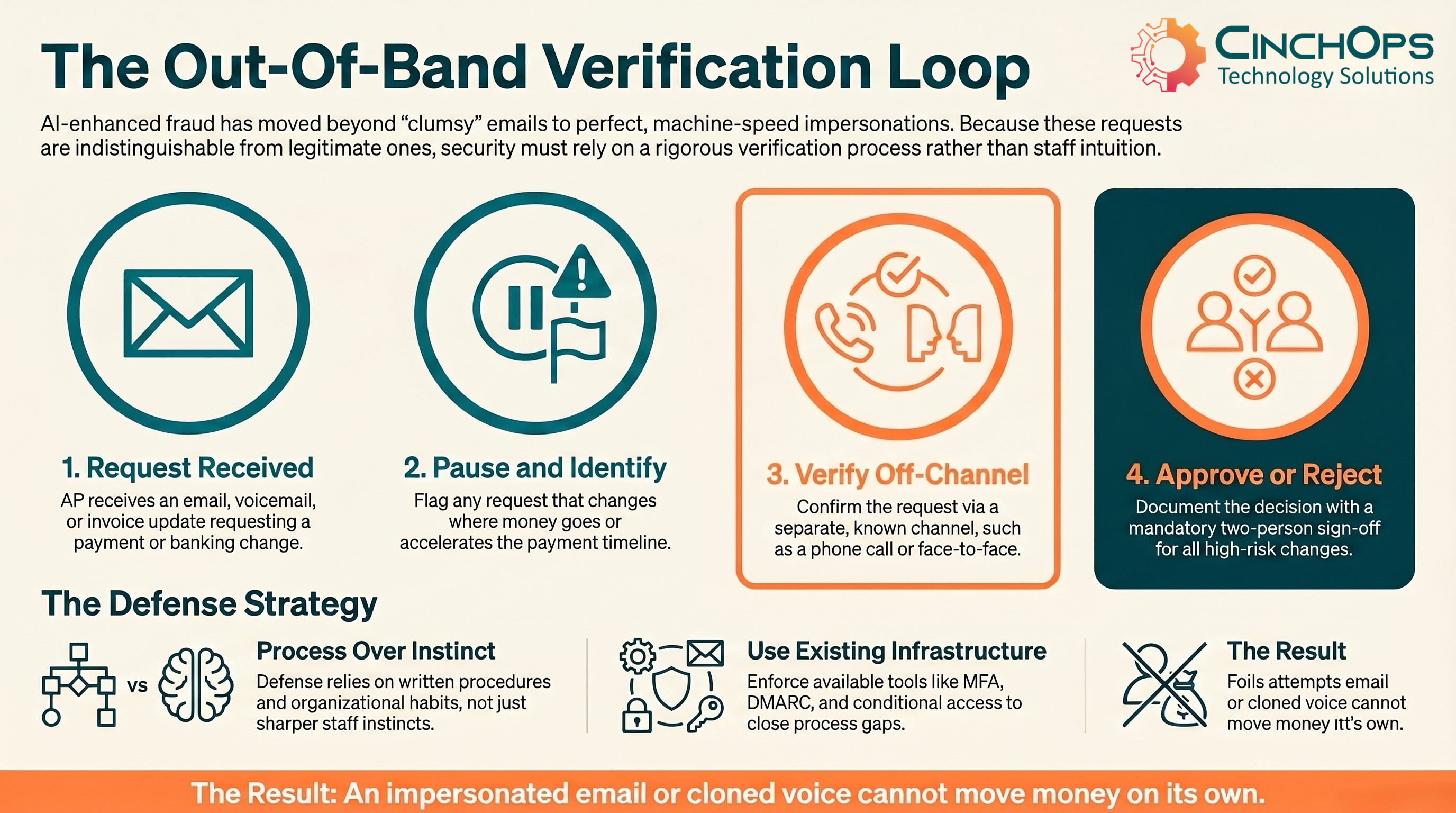
When a fraudulent request is genuinely indistinguishable from a legitimate one, putting the burden of detection on the AP team is putting it in the wrong place. Houston businesses that reduce risk are not asking staff to be more suspicious. They are building verification processes that work independent of how a message looks.
Concerned About Your AP Process?
CinchOps reviews payment workflows and verification controls for Houston-area finance teams. No sales pitch, no obligation.
Talk to CinchOps →Build Process Around the Risk
The most effective defense isn't sharper instincts. It's removing ambiguity from high-risk actions. Three changes do most of the work.
- Out-Of-Band Verification As Standard. Any request to change supplier bank details or approve an urgent payment outside the normal cycle requires secondary confirmation through a known, independent channel. Not a reply to the same email thread. Calling a supplier on a number already on file, or confirming with a colleague directly, breaks the impersonation chain regardless of how convincing the original request looked.
- Layered Access And Authentication Controls. Restricting access to financial systems and enforcing multi-factor authentication limits the damage a compromised account can cause. If an attacker gains access to a vendor's email, MFA on the receiving end creates friction that can slow or stop a fraudulent change before any money moves.
- A Culture That Supports Slowing Down. Fraud prevention improves when staff feel safe questioning requests, including from senior leadership. A team member who pauses a payment to verify it isn't being obstructive, they're doing exactly what good process requires. That culture starts with leadership modeling the behavior and making clear that slowing down on high-risk actions is always the right call.
None of these are technology purchases. They are written procedures, organizational habits, and access controls. The technology supporting them, MFA, conditional access, email authentication, is already available in the tools most Houston businesses already pay for.
How AI Fraud Hits Houston Industries Differently
The risk profile shifts based on how a business pays vendors and who has approval authority. Here's where AP fraud lands hardest across Houston-area sectors.
| Industry Sector | Primary Risk | Growth Pressure | Strategic IT Focus |
|---|---|---|---|
| Construction | Vendor bank-change scams during active projects | Tight margins, fast payment cycles | Verified supplier portal, MFA on email |
| CPA Firms | Client wire fraud during tax season peaks | Compliance and FTC Safeguards Rule | Out-of-band approval, audit logging |
| Law Firms | Trust account redirection, client identity spoofing | Bar compliance, client confidentiality | Email authentication, identity controls |
| Wealth Management | Voice-cloned client transfer requests | FINRA/SEC reporting, reputational risk | Voice verification protocols, MFA |
| Oil & Gas | Large-dollar invoice substitution from contractors | Supply chain volatility, JV billing | Vendor master file controls, segregation |
| Manufacturing | Distributor and parts-supplier impersonation | Supply chain reliability, just-in-time inventory | Supplier verification, AP automation review |
Across all six sectors, the underlying weakness is the same. Payment authority is delegated to AP staff who need to move quickly, and verification depends on the same channel the request arrived on. Closing that gap requires changes to process. The technology to support it is already in place at most businesses, just not turned on or enforced.
How CinchOps Helps Houston Businesses Defend AP
CinchOps works with Houston-area finance and operations leaders to harden the parts of the business where AI-enhanced fraud actually lands. The work is part technical, part procedural, and starts with a review of how payments flow through the organization today.
- Email Authentication and Inbound Filtering. Properly configured DMARC, SPF, and DKIM records, plus an email security layer tuned for impersonation patterns rather than just spam. This catches a large share of spoofed sender attempts before they reach AP.
- Multi-Factor Authentication Across Finance Systems. MFA on email, accounting platforms, banking portals, and any system that holds vendor master data. Not just for admins, for every user with payment authority.
- Written Verification Procedures. CinchOps helps draft and document the out-of-band verification process so it's a defined organizational standard, not a habit that disappears when someone is on vacation.
- Vendor Master File Controls. Periodic review of who can change supplier banking details, segregation of duties between vendor setup and payment approval, and logging of all changes.
- Tabletop Exercises and Awareness. Realistic scenario walkthroughs with AP and finance staff. Not generic phishing training, specific run-throughs of the kinds of impersonation attempts targeting Houston businesses right now.
The goal is simple. Make sure no single email, voicemail, or phone call, no matter how convincing, can move money on its own. That's what good cybersecurity looks like for an AP team in 2026.
✓ Quick Self-Assessment for Houston Finance Leaders
- Does your team verify any vendor bank-detail change through a second, independent channel (phone call to a known number) before updating the master file?
- Is multi-factor authentication enforced on every email account with access to invoices, payment approvals, or banking portals?
- Do you have a written procedure for handling urgent payment requests from executives, and does the procedure require off-channel confirmation?
- Has your team practiced a tabletop scenario for an AI-cloned voicemail or BEC email in the past 12 months?
- If a payment goes out fraudulently, do you know who to call and what bank actions to take in the first 60 minutes?
Frequently Asked Questions
Discover More From CinchOps
Sources
- FBI 2025 Internet Crime Report (IC3): Business email compromise cost US businesses more than $3 billion in 2024, with $893 million in AI-enabled scam losses across 22,000+ complaints.
- FBI Internet Crime Complaint Center: BEC attacks rely on impersonation, posing as trusted executives, suppliers, or colleagues to redirect payments.
- Industry research, mid-2024: An estimated 40% of BEC phishing emails are AI-generated, with that share expected to grow significantly.





