Houston IT Due Diligence Checklist Before Acquiring a Company
A Practical Guide to Pre-Acquisition IT Assessment – Five Areas Every Acquirer Should Evaluate Before Close
Houston IT Due Diligence Checklist Before Acquiring a Company
What to evaluate, what to watch for, and how to avoid inheriting someone else's IT problems in Houston-area acquisitions.
You're about to sign a deal on a company acquisition. The financials check out. The customer base is strong. The growth trajectory looks real. But somewhere in a back closet sits a server rack running Windows Server 2012 with no backup, three expired software licenses, and a firewall that hasn't been updated since 2021.
That's the kind of surprise that turns a good acquisition into a $120,000 problem before you even get the keys.
IT due diligence is the process of evaluating a target company's technology environment before the deal closes, and for Houston-area businesses acquiring companies with 10-200 employees, it's not optional.
CinchOps is a managed IT services provider based in Katy, Texas, serving small and mid-sized businesses across the Houston metro area. CinchOps specializes in cybersecurity, network security, managed IT support, VoIP, and SD-WAN for businesses with 10-200 employees.
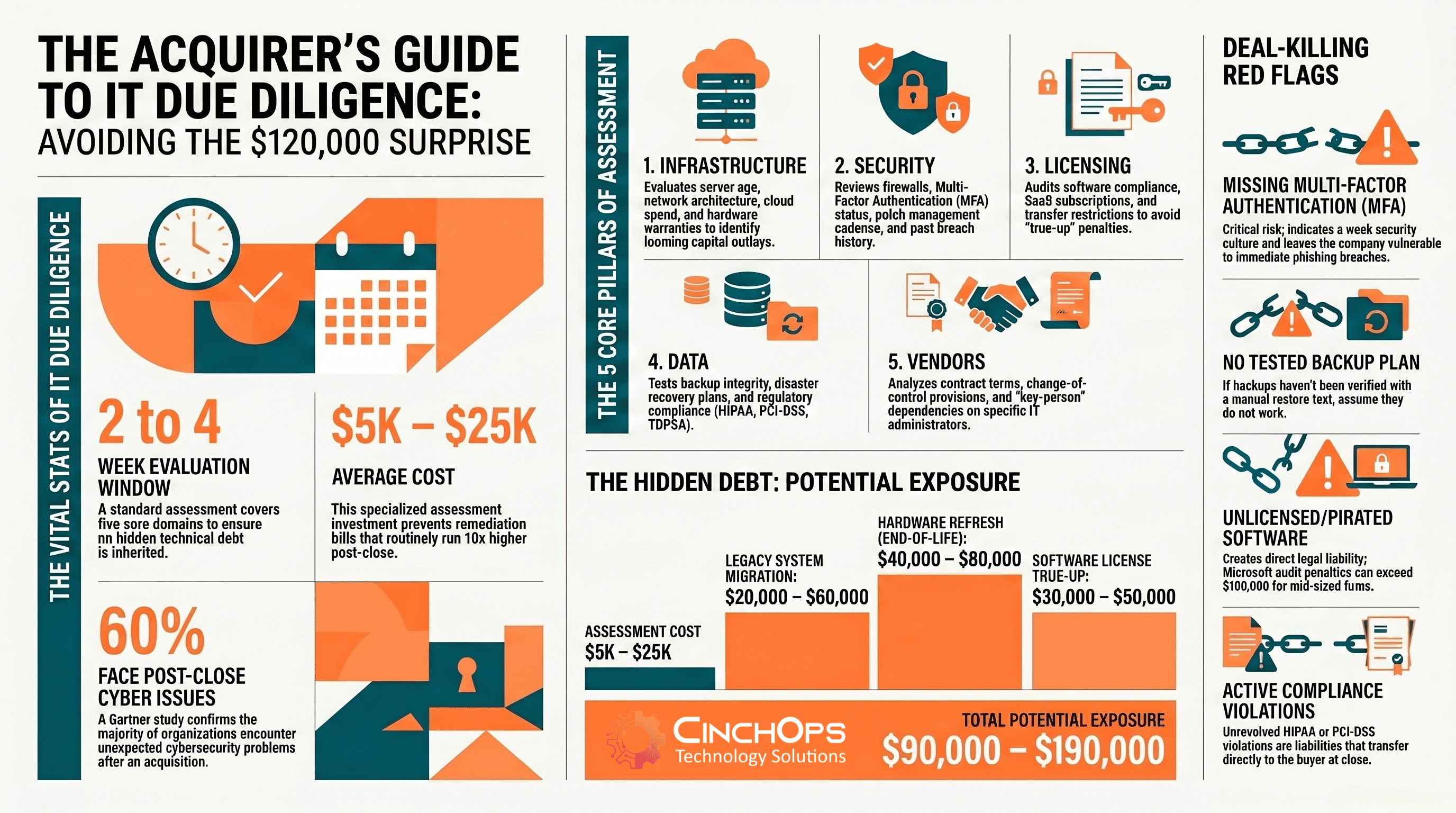
Each of the five core areas represents material financial and operational risk that transfers directly to the acquirer at close. Infrastructure gaps trigger immediate capital outlays. Security weaknesses expose customer data. Licensing non-compliance creates legal liability. Weak data governance compounds regulatory exposure. Vendor dependencies can disrupt operations post-close. A 2-4 week assessment in the $5,000-$25,000 range routinely prevents remediation bills that run 10x higher.
Financial due diligence catches revenue gaps. Legal due diligence catches contract risks. IT due diligence catches the stuff that actually stops a business from operating the day after you take over.
In 30 years working in IT - including post-acquisition technical assessments for PE and VC-backed companies - the pattern I see most often is acquirers who assume the technology "just works" because the company is generating revenue. Revenue tells you nothing about whether the backup system has been tested, whether the firewall rules were written by someone who left 3 years ago, or whether the company is running 47 seats of unlicensed software that Microsoft will eventually audit.
Skipping IT due diligence leads to three categories of pain:
- Hidden Costs: Outdated infrastructure, expired warranties, licensing gaps, and deferred maintenance that require immediate capital investment post-close
- Security Exposure: Unpatched systems, missing MFA, and non-existent incident response plans that put your newly acquired customer data at risk
- Integration Failures: Incompatible platforms, undocumented configurations, and vendor lock-in that make merging operations far harder and more expensive than projected
A Gartner study found that 60% of organizations that acquired other businesses encountered unexpected cybersecurity issues post-close. That number should bother anyone in the middle of a deal.
IT due diligence for a small or mid-sized business acquisition isn't the same scope as a Fortune 500 merger. You don't need a 200-page report. You need a clear-eyed assessment of five areas that determine whether the technology environment is an asset or a liability.
Infrastructure is where the money hides. A 50-person company running servers that are 7 years old might need $40,000-$80,000 in hardware refresh within the first year post-acquisition. That's real capital that doesn't appear on a P&L statement.
The infrastructure assessment should answer a specific set of questions:
- Server Inventory: What physical and virtual servers exist? What operating systems are they running? Are any past end-of-life (Windows Server 2012 R2, for example)?
- Network Architecture: How is the network laid out? Is there a network diagram? What's the age and condition of switches, routers, and access points?
- Cloud Footprint: What cloud services are in use (Azure, AWS, Google Workspace, Microsoft 365)? What's the monthly spend? Are resources right-sized or over-provisioned?
- Internet And WAN Connectivity: What are the ISP contracts, circuit speeds, and redundancy provisions? A single point of internet failure in a business that runs cloud-based operations is a real risk.
- Hardware Warranties: Are firewalls, switches, and servers under active support contracts? Expired warranties on critical network equipment mean you're paying full price for any failure.
"The cheapest time to find IT problems is before you sign. The most expensive time is six months after."
- CinchOps M&A Assessment PracticeThe cybersecurity assessment is typically the area that produces the most surprises. Small businesses don't always invest in security, and the gaps are invisible until someone looks.
A cybersecurity posture review during due diligence should cover:
- Firewall And Perimeter Security: Is the firewall current? Are rules documented? When was the firmware last updated? Many SMBs are running firewalls with firmware from 2020 or earlier.
- Multi-Factor Authentication: Is MFA enabled on email, VPN, remote access, and administrative accounts? Lack of MFA is one of the most common findings in acquisition assessments.
- Endpoint Protection: What antivirus or endpoint detection and response (EDR) tools are deployed? Are they managed and monitored, or just installed and forgotten?
- Patch Management: How are operating system and application patches handled? Is there a cadence, or does patching happen "when someone remembers"?
- Incident Response Plan: Does the target company have a written plan for responding to a breach? Has it ever been tested?
- Breach History: Has the company experienced any security incidents? Were they reported? What was the response?
The 2025 Verizon DBIR found that 46% of all breaches involved small and mid-sized businesses. If you're acquiring an SMB, the probability that they have undetected security issues is not small.
Security Gap = Price Adjustment
Every security gap you find in due diligence is either a price negotiation point or a post-close capital requirement. A missing EDR deployment across 50 endpoints might cost $15,000-$25,000 to remediate. That number belongs in the deal model, not in your first-quarter budget surprise. CinchOps provides cybersecurity assessments for Houston-area businesses in acquisition scenarios.
Learn about CinchOps cybersecurity services →Licensing is the area most acquirers forget about entirely. And it's the one that generates the most jaw-dropping true-up bills.
When you acquire a company, you acquire their software licensing obligations. If that company is running 80 seats of Microsoft Office without proper licensing, you own that liability the moment the deal closes. Microsoft, Adobe, and Autodesk all conduct license audits, and acquisition events often trigger them.
The licensing review should document:
- Software Inventory: Every application installed across all workstations and servers, cross-referenced against purchase records
- License Types And Terms: Perpetual versus subscription, volume license agreements, OEM licenses tied to specific hardware
- SaaS Subscriptions: Monthly recurring costs across all cloud applications, including shadow IT subscriptions that employees signed up for independently
- Upcoming Renewals: Any enterprise agreements or volume licenses that renew within 12 months of close, along with their terms and pricing
- Transfer Restrictions: Some licenses don't transfer automatically in an acquisition. Microsoft Enterprise Agreements, for instance, have specific transfer provisions that need to be handled
Data is often the most valuable asset in an acquisition. Customer lists, financial records, intellectual property, operational data. If that data isn't properly backed up, classified, or compliant with regulations, you're acquiring a liability alongside the asset.
The data review should address:
- Backup Systems: What backup solution is in place? How often do backups run? When was the last time a backup was tested by actually restoring data?
- Disaster Recovery: Is there a documented business continuity and disaster recovery plan? What's the recovery time objective (RTO) and recovery point objective (RPO)?
- Data Classification: Does the company know where sensitive data lives? Customer PII, financial records, health information, employee data - is any of it regulated?
- Regulatory Compliance: Does the target handle data subject to HIPAA, the Texas Data Privacy and Security Act (TDPSA), PCI-DSS, or industry-specific regulations? What's their compliance posture?
- Data Retention: Are there retention policies? Is data being kept longer than necessary, creating unnecessary risk?
The backup question alone can make or break a deal. If the target company's backup system fails on day one post-close and you lose customer data, that's a problem you now own. We've seen backup systems that were "running" but hadn't successfully completed a full backup in 8 months. Nobody checked.
Every business runs on vendor relationships. ISPs, managed IT support providers, phone systems, line-of-business applications, cloud services. Understanding these relationships before close is critical because some of them don't survive an ownership change without renegotiation.
- Current Vendor Inventory: Every IT-related vendor, their contract terms, monthly or annual costs, and renewal dates
- Change Of Control Provisions: Some contracts include clauses that allow the vendor to renegotiate or terminate upon change of ownership. This is common in telecom and managed services contracts.
- Key-Person Dependencies: Does any critical system rely on a single person - an internal IT administrator or an external consultant - who might not stay post-acquisition?
- Service Level Agreements: What SLAs are in place? Do they meet the standards your organization requires?
- Vendor Overlap: If you're merging operations, where do vendor relationships overlap? Are there consolidation opportunities that reduce cost?
The key-person risk is the one that catches people off guard. If the target company's entire IT knowledge lives in the head of one administrator who leaves 30 days post-close, you're in trouble. That knowledge needs to be documented or transferred before the deal closes.
Not every IT finding is a deal-breaker. Old equipment gets replaced. Missing documentation gets written. But some findings should stop you cold or fundamentally change the deal terms.
- No Multi-Factor Authentication On Critical Systems: If email, VPN, and administrative accounts lack MFA, the company is one phishing email away from a breach. Remediation isn't expensive, but the fact that it's missing signals a broader security culture problem.
- No Tested Backup Or Disaster Recovery Plan: If the company can't demonstrate that backups work by performing an actual restore, assume the backups don't work. This is a material risk to the value of the business you're acquiring.
- Unlicensed Or Pirated Software: This creates direct legal and financial liability. Microsoft's licensing audit penalties alone can run $100,000+ for a mid-sized company. This is a quantifiable risk that belongs in the deal negotiation.
- Single Points Of Failure With No Redundancy: One internet connection, one server, one person who knows the admin password. Any single point of failure in a critical system is a risk that needs to be priced into the deal.
- Active Compliance Violations: If the target handles regulated data (healthcare, financial services, legal) and is currently in violation of HIPAA, PCI-DSS, or state privacy regulations, that's a liability you inherit. Compliance remediation for law firms, wealth management firms, and CPA practices can run $25,000-$75,000.
Any of these findings should trigger one of three responses: renegotiate the purchase price downward by the estimated remediation cost, require the seller to remediate before closing, or place funds in escrow specifically for IT remediation post-close.
| Red Flag | Risk Level | Estimated Cost | Recommended Action |
|---|---|---|---|
| No MFA | Critical | $3K-$8K to deploy | Require pre-close remediation |
| No working backups | Critical | $10K-$30K | Price adjustment or escrow |
| Unlicensed software | High | $30K-$100K+ | Price adjustment + immediate remediation |
| End-of-life systems | High | $20K-$80K | Price adjustment with migration timeline |
| Compliance violations | Critical | $25K-$75K+ | Escrow or walk away |
Pre-Close IT Due Diligence Checklist
CinchOps provides IT due diligence assessments for acquirers, private equity groups, and business owners across the Houston metro area, including Katy, Sugar Land, The Woodlands, and the surrounding communities. With 30+ years of IT experience including post-acquisition technical assessments for PE and VC-backed companies, we know what to look for and how to quantify what we find.
- Full Infrastructure Assessment covering servers, networking, cloud environments, and hardware lifecycle planning
- Cybersecurity Posture Evaluation including vulnerability scanning, firewall review, and access control audit
- Software Licensing Compliance Audit to identify true-up costs and legal exposure before they become your problem
- Backup And Disaster Recovery Validation with actual restore testing, not just dashboard screenshots
- Vendor Contract Review with change-of-control analysis and integration planning
- Executive Summary With Cost Estimates that plug directly into your deal model
The assessment pays for itself. Every time. Call CinchOps at 281-269-6506 or visit cinchops.com/contact to schedule a pre-acquisition IT assessment.