
Cybersecurity Katy: What the BlackFog Q1 2026 Ransomware Numbers Tell Houston Businesses
Industry-by-Industry Look at Q1 2026 Ransomware Activity – Manufacturing, Construction, Healthcare: Houston’s Sectors Are on the List
Cybersecurity Katy: What the BlackFog Q1 2026 Ransomware Numbers Tell Houston Businesses
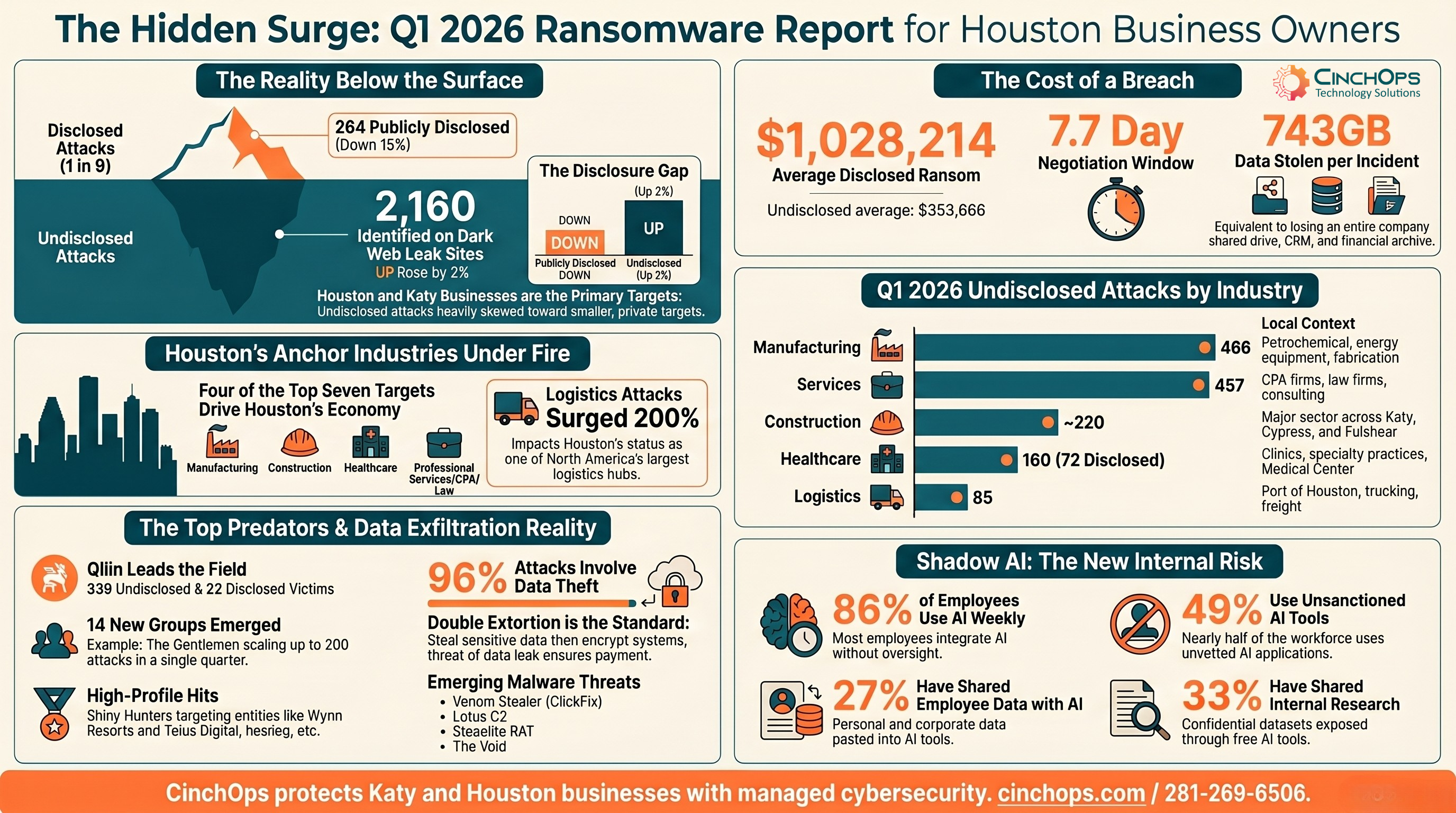
BlackFog tracked 264 publicly disclosed and 2,160 undisclosed ransomware attacks in Q1 2026. For Katy and Houston business owners, the numbers below the surface are the ones that matter.
BlackFog's Q1 2026 State of Ransomware report tracked 264 publicly disclosed ransomware attacks and 2,160 undisclosed attacks recorded on dark web leak sites. The disclosed number is down 15% year-over-year. The undisclosed number is up. That gap is the story for any Katy business owner thinking about cybersecurity in 2026.
Most ransomware attacks never make the news. Only one in nine becomes public. The rest get settled quietly, or victims pay without ever telling regulators, customers, or insurers what happened. Cybersecurity in Katy isn't a question of whether your industry is on the target list. It is. The real question is whether you can see an attacker inside your network before they finish exfiltrating your data.
Disclosed ransomware attacks are incidents that companies, regulators, or law enforcement confirm publicly. Undisclosed attacks are the ones BlackFog identifies on ransomware group leak sites, where threat actors post stolen data to pressure victims. In Q1 2026, BlackFog counted 264 disclosed incidents and 2,160 undisclosed ones. That is roughly 9 attacks happening for every 1 the public hears about.
For small and mid-sized businesses in Katy, this matters because undisclosed attacks are skewed toward smaller targets. Larger, publicly traded companies have SEC reporting obligations and ransomware disclosure rules. A 60-person engineering firm in west Houston that gets hit, pays a $200,000 ransom, and quietly restores from backup never shows up in a headline. It shows up in the BlackFog numbers.
- Disclosed Attacks. 264 incidents, down 15% from 303 in Q1 2025.
- Undisclosed Attacks. 2,160 incidents, up 2% from 2,125 a year earlier.
- Ratio. Only 1 in 9 ransomware attacks becomes publicly known.
- Active Groups. 79 distinct ransomware groups claimed victims in the quarter, with 14 new ones emerging.
- Geographic Scope. Organizations in 97 countries were hit, including small nations like Andorra, Mauritius, Panama, and Namibia.
The ransomware drop in disclosed attacks isn't progress. It's a reporting gap. Threat actors are quieter, more targeted, and more focused on data theft than encryption noise that would force a disclosure.
The industries that took the worst hits in Q1 2026 line up almost perfectly with Houston's economic base. Manufacturing, services, construction, energy, healthcare, and finance dominated the attack data. Katy itself sits in the middle of the construction and energy services corridor, with hundreds of small and mid-sized firms supporting the larger Houston operators.
| Industry | Disclosed Attacks | Undisclosed Attacks | Houston Exposure |
|---|---|---|---|
| Manufacturing | ~25 (9%) | 466 (22%) | Petrochemical, fabrication, energy equipment |
| Services | ~22 (8%) | 457 (21%) | Professional services, BPO, consulting |
| Construction | ~3 (1%) | ~220 (10%) | Major sector across Katy, Cypress, Fulshear |
| Healthcare | 72 (27%) | ~160 (7%) | Medical Center, clinics, specialty practices |
| Technology | 28 (11%) | ~180 (8%) | SaaS, MSPs, software firms |
| Finance | ~10 (4%) | ~140 (6%) | Banks, wealth managers, CPA firms |
| Logistics | 5 (2%) | ~85 (4%) | Port of Houston, trucking, freight (up 200% YoY) |
Healthcare's disclosed-attack lead is partly a reporting artifact. HIPAA and state notification laws make hospital breaches almost impossible to keep quiet. Manufacturing topping the undisclosed list says something different: operational technology environments are getting hit at scale, and most of those attacks never reach the news. Anyone running a manufacturing plant in the Houston ship channel area or a fabrication shop in Brookshire or Sealy should treat that number as a personal warning.
"The Katy businesses I worry about most aren't the ones reading about big-name ransomware hits in the news. It's the small construction and energy services firms that don't realize they're already on a target list. The undisclosed numbers tell you what's really happening on the ground."
The logistics spike is also worth noting. Logistics attacks surged 200% year-over-year in Q1 2026. Houston is one of the largest logistics hubs in North America. The Port of Houston handles more foreign tonnage than any other U.S. port. Every Katy firm with a logistics, freight, or warehousing tie is exposed to this trend, directly or through vendor relationships.
BlackFog logged an average disclosed ransom demand of $1,028,214 in Q1 2026. The undisclosed average was $353,666. The disclosed average is skewed by a handful of multi-million dollar demands against large enterprises. The undisclosed number is closer to what a mid-sized Katy business should actually budget for if they're trying to model worst-case exposure.
Average data exfiltration reached 743GB per incident. That is, on average, the equivalent of a mid-sized company's entire shared drive, CRM, financial system, and email archive walking out the door. The average negotiation deadline was just 7.7 days. Threat actors aren't giving victims time to think.
- Disclosed Average Ransom. $1,028,214.
- Undisclosed Average Ransom. $353,666.
- Average Data Exfiltrated. 743GB per incident.
- Negotiation Deadline. 7.7 days on average.
- Data Exfiltration Rate. 96% of attacks involved data theft, holding at an all-time high.
Here's the part that catches Katy business owners off guard: the ransom is rarely the biggest cost. IBM's 2025 Cost of a Data Breach report put the average SMB breach cost at $4.88 million when you add up downtime, recovery, legal exposure, regulatory penalties, customer notification, and credit monitoring. The ransom demand is just the opening bid.
Want to Know Your Risk?
CinchOps offers free security assessments for Katy and Houston-area businesses. No commitment, no contract.
Get a Free AssessmentData exfiltration is the theft of sensitive files from a network, usually staged before any encryption happens. In Q1 2026, 96% of ransomware attacks involved data exfiltration, holding steady from the 2025 spike. The ransomware groups that dominated this quarter (Qilin, The Gentlemen, Akira, Sinobi, Shiny Hunters) all default to double extortion: steal first, encrypt second, then threaten to leak the data if the ransom isn't paid.
BlackFog also flagged four emerging threats worth attention from any Katy business with employees handling sensitive data:
- Venom Stealer. A ClickFix-based credential and session cookie stealer delivered through fake CAPTCHA prompts. Once active, it captures new data in real time, not just at the moment of compromise.
- Lotus C2. A pre-configured command-and-control framework marketed as a ready-to-use cybercrime kit. Lowers the technical bar for less sophisticated attackers.
- Steaelite RAT. Combines remote access, data theft, and extortion in a single control panel. One tool, one operator, full attack chain.
- The Void. A malware-as-a-service infostealer sold on underground markets. Targets credentials, browser data, and crypto wallets at scale.
The Shadow AI angle deserves its own paragraph. Shadow AI is the use of unsanctioned generative AI tools by employees, often without IT awareness. BlackFog's research found 86% of employees use AI tools weekly at work, 49% use tools not approved by their employer, 27% have shared employee data with AI tools, and 33% have shared internal research or datasets. For a Katy CPA firm or wealth management practice handling client financials, that's a regulatory time bomb sitting on every employee's laptop.
Threat actors are no longer just encrypting your files. They're stealing your data and using your own employees' unmanaged AI use against you. Both attack paths bypass traditional antivirus and require active monitoring, not just prevention.
CinchOps is a managed IT services provider based in Katy, Texas, serving small and mid-sized businesses across the Houston metro area. CinchOps specializes in cybersecurity, network security, managed IT support, VoIP, and SD-WAN for businesses with 10 to 200 employees, including construction, CPA firms, manufacturing, and wealth management firms.
Based on the Q1 2026 attack data, here's how CinchOps protects Katy businesses against the threats that did the most damage:
- Endpoint Detection And Response. CinchOps deploys advanced EDR across every laptop, server, and workstation. We watch for the abuse of legitimate admin tools (Qilin, The Gentlemen, and Akira all rely on this technique).
- Data Exfiltration Monitoring. With 96% of attacks involving data theft, blocking outbound data flows matters more than blocking encryption. CinchOps deploys anti-exfiltration controls on every endpoint.
- Patch Management. Most ransomware entry points are known vulnerabilities that went unpatched. CinchOps runs weekly patch cycles with verification, not just push-and-hope.
- Backup And Recovery. Air-gapped, immutable backups with documented business continuity and disaster recovery procedures. Ransomware loses leverage when you can rebuild fast.
- Employee Phishing And Shadow AI Training. ClickFix and fake CAPTCHA attacks rely on user clicks. We train your team on what to watch for and write usage policies for AI tools.
- Multi-Factor Authentication Everywhere. Including for VPN, remote desktop, email, and admin accounts. ShinyHunters' Telus and Wynn Resorts breaches both leveraged compromised credentials.
- 24/7 Monitoring. The Q1 2026 average negotiation deadline was 7.7 days. Detection in hours, not weeks.
Cybersecurity in Katy isn't about buying the most products. It's about layering the right controls and having someone watching them at 2 a.m. when an attacker decides to deploy. That's what CinchOps does for small and mid-sized businesses across Katy, Cypress, Fulshear, Sugar Land, and the broader Houston area.
Cybersecurity Katy Self-Assessment Checklist
- You have endpoint detection and response (EDR) deployed on every workstation, laptop, and server, not just antivirus.
- You can name your last successful backup test. Not "we have backups", but a real restore drill in the last 90 days.
- Multi-factor authentication is required for VPN, remote desktop, email, and any admin account.
- You have a written policy on what AI tools employees can and can't use with company or client data.
- You patch critical vulnerabilities within 7 days, with verification that the patch actually took.
- Someone is reviewing security alerts after hours, on weekends, and during holidays.
- You have an incident response plan that has been tested in the last 12 months.
- You know what data leaves your network on an average day, and you can stop unusual outbound transfers.
Frequently Asked Questions
What is the state of ransomware in Q1 2026 according to BlackFog?
BlackFog's Q1 2026 State of Ransomware report tracked 264 publicly disclosed ransomware attacks and 2,160 undisclosed attacks identified on dark web leak sites. Healthcare led disclosed attacks at 27%. Manufacturing led undisclosed attacks at 22%. Data exfiltration occurred in 96% of attacks, and 14 new ransomware groups emerged.
Why does cybersecurity matter for Katy businesses specifically?
Cybersecurity in Katy matters because Katy sits in the Houston metro corridor, surrounded by the construction, energy services, manufacturing, and healthcare sectors that ransomware groups targeted most aggressively in Q1 2026. Small and mid-sized businesses in these industries are heavily represented in the 2,160 undisclosed ransomware attacks BlackFog tracked this quarter.
What is the difference between disclosed and undisclosed ransomware attacks?
Disclosed ransomware attacks are incidents publicly confirmed by victim organizations, regulators, or law enforcement, often required by SEC, HIPAA, or state data breach laws. Undisclosed attacks are incidents identified on ransomware group leak sites where threat actors post stolen data. BlackFog data shows only 1 in 9 ransomware attacks becomes publicly known.
How much does the average ransomware attack cost a small business?
BlackFog's Q1 2026 data shows the disclosed average ransom demand was $1,028,214 and the undisclosed average was $353,666. But the ransom is rarely the largest cost. IBM's 2025 Cost of a Data Breach report puts the average SMB breach total cost at $4.88 million when factoring in downtime, recovery, regulatory penalties, and customer notification.
What can a Katy business do to defend against ransomware right now?
Katy businesses should deploy endpoint detection and response (EDR) on every device, require multi-factor authentication on all remote access, run verified weekly patch cycles, maintain immutable air-gapped backups, monitor outbound data flows for exfiltration, train employees on phishing and AI tool risks, and ensure someone reviews security alerts 24/7. CinchOps delivers all of these as a managed service.
Discover More
Resources
Sources
- BlackFog State of Ransomware Q1 2026 Report - 264 disclosed attacks, 2,160 undisclosed attacks, 96% data exfiltration rate, $1,028,214 average disclosed ransom demand
- BlackFog Q1 2026 - The Gentlemen ransomware group profile, Qilin, Shiny Hunters, INC variant attack distribution
- BlackFog Q1 2026 - Industry breakdown: Healthcare 27% disclosed, Manufacturing 22% undisclosed, Logistics surged 200% YoY
- BlackFog Q1 2026 - Emerging threats: Venom Stealer, Lotus C2, Steaelite RAT, The Void infostealer
- BlackFog Q1 2026 Shadow AI Research - 86% weekly AI use, 49% unsanctioned tools, 27% sharing employee data with AI
- IBM Cost of a Data Breach Report 2025 - $4.88 million average SMB breach cost





