When Hackers Learn to Speak Machine: ‘Living-off-the-Plant’ Attacks Could Change OT Security Forever
The Next Cyberattack Won’t Come Through Email – It’ll Come Through Your HVAC
When Hackers Learn to Speak Machine:
‘Living-off-the-Plant’ Attacks Could Change OT Security Forever
![]()
TL;DR: Security researchers are warning that attackers are gaining an ever closer grip on industrial control systems, evolving from crude break-ins to “living-off-the-plant” attacks that use OT environments’ own tools against them. Recent incidents at water facilities, dams, and power utilities signal the shift, and small businesses with industrial or building management systems should be paying attention now.
![]()
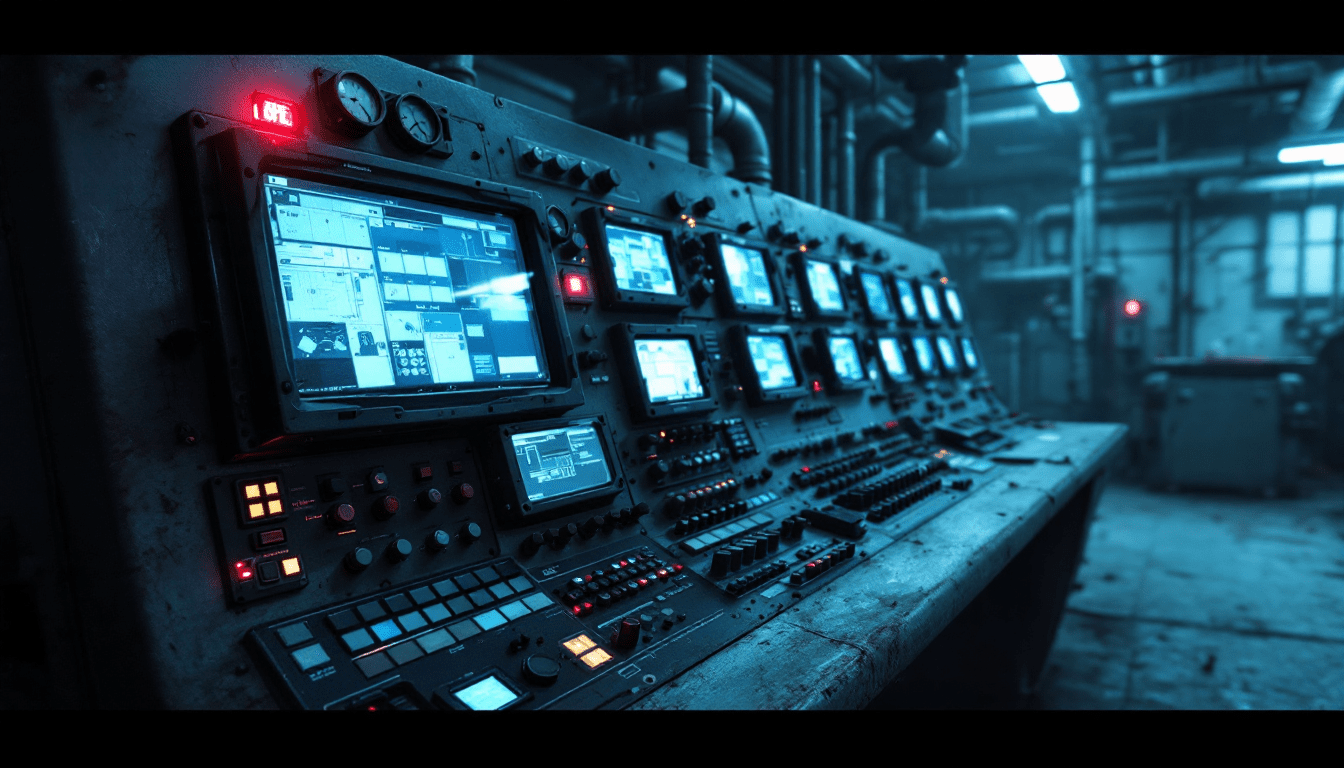
We have had an odd kind of luck in the past decade with attacks on operational technology. Once they made it up to an industrial control system, the hackers that got there largely didn’t know what to do. They stumbled around, pressed buttons at random across a human-machine interface, or simply made a defacement message and disappeared. That luck seems to be waning.
Ric Derbyshire, the principal security researcher at Orange Cyberdefense and honorary researcher at Imperial College London, popularized the phrase “living-off-the-plant” to refer to what he deems the next phase of OT attacks. At the next RSAC 2026 Conference in San Francisco in March, he intends to show just how lethal things could turn out once attackers know what industries they’re penetrating.
Living-off-the-Land vs. Living-off-the-Plant:
How Do They Differ?
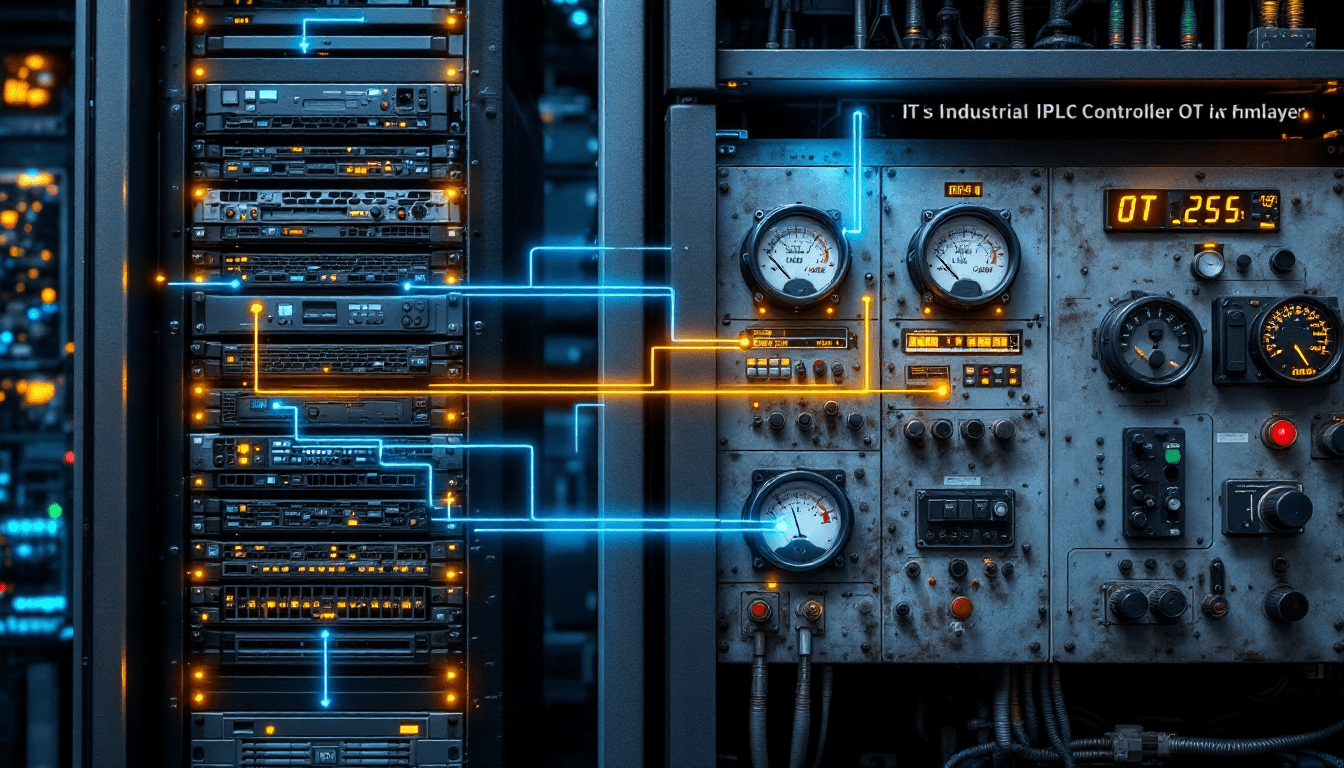
IT pros generally know about “living-off-the-land” attacks. This means the attackers just use things that are already accessible on the compromised system, things such as PowerShell, WMI, and other built-in Windows utilities, to get their way without using malware.
- In a 2025 study of over 700,000 incidents, 84% of major attacks used these techniques
- PowerShell accounted for 71% of those cases
“Living-off-the-plant” brings that to the industrial realm. Rather than exploiting Windows utilities, the attackers would use the OT environment’s own protocols, engineering software, and control system functions to manipulate physical processes. This is like a burglar with your own kitchen knife vs one who knows how to rewire your entire electrical system.
The reason we haven’t observed this on a very large scale to date comes down to what Derbyshire describes as “process comprehension.” Attackers who get inside OT systems usually don’t know how industrial processes actually work. Every enterprise IT network does more or less the same everywhere. But a consumer goods manufacturing plant and 50-year-old water treatment plant could as well be on another planet.
Real Incidents Demonstrate That Attackers
Are Getting Bolder
Multiple recent incidents indicate attackers are moving ever closer to that process understanding, even if they’re not quite there yet.
Norway Dam Breach (April 2025): Hackers accessed a dam at Lake Risevatnet in western Norway through a web-accessible HMI protected by a weak password. They opened a water valve to 100% capacity, unleashing an additional 497 liters per second for four hours before anyone noticed. The Russian-linked hacktivist group Z-PENTEST took responsibility. No harm was done physically, because the dam could handle 20,000 liters per second, but the attackers showed they could take physical infrastructure and alter it with mere access. As Derbyshire put it, they discovered default credentials, logged on and clicked around with rudimentary functionality. Scary, but crude.
CyberAv3ngers and U.S. Water Systems (2023): Iranian IRGC-affiliated hackers posing as “CyberAv3ngers” infiltrated Unitronics Vision Series PLCs at multiple U.S. water facilities, such as the Municipal Water Authority of Aliquippa in Pennsylvania. They took advantage of default passwords (the factory default was “1111”) on internet-facing devices. The attackers left defacement messages, but also developed custom ladder logic files and tried to hack the devices down the wire. CISA, the FBI, and NSA issued joint advisories warning that this kind of access could have deeper cyber-physical effects.
Volt Typhoon’s Long Game: Chinese state-sponsored hackers kept undetected access to the Littleton Electric Light and Water Department in Massachusetts for close to 300 days until detection in late 2023. Dragos, the OT security firm that probed, found that the group was particularly stealing geographic information system data, operating procedures, and spatial layout details about energy grid operations. They didn’t mean to get customer data or ransom money. They were mapping infrastructure for potential future disruption. CISA confirmed that Volt Typhoon had been in some victims’ installations for at least 5 years, and used default vendor credentials for testing access to OT assets.
Why This Is Getting Worse
Derbyshire says attackers are learning process intelligibility more rapidly than a lot of people know. There are textbooks, artificial intelligence chatbots, and secondhand PLCs listed on e-marketplaces. OpenAI had just released an investigation in which it revealed that CyberAv3ngers actors were using ChatGPT to query default usernames and password settings for industrial equipment. The leap from “what are the default credentials” to “how does this protocol operate” is not a huge one.
At RSAC 2026, Derbyshire will deliver a demonstration of how an attacker might weaponize S7comm, Siemens’ proprietary communications protocol for PLC devices. By manipulating configuration fields we don’t usually pay attention to, an attacker could leak sensitive data and spread attacks across different devices. He’s dubbing it “an absolute brain melter.”
Ironically, OT’s diversity, that each plant is just its own unique patchwork of different decades’ equipment, has been a sort of accidental security measure. But that doesn’t last. Every older water treatment site, every HVAC system running legacy controllers, every manufacturing floor equipped with internet-connected PLCs is a potential target once attackers gather enough general OT information.

Who Is at Risk?
This is not just an issue for power plants and water utilities. Exposure is possible for any organization that has operational technology or industrial control systems.
- Manufacturing companies with PLCs, SCADA systems, or automated production lines
- Building management systems controlling HVAC, elevators, and access control
- Water and wastewater facilities, particularly small municipal operations with low IT budgets
- Energy industry companies including oil and gas operations typical throughout the Houston and Texas Gulf Coast area
- Healthcare providers with interconnected building systems and medical device networks
- Food and beverage producers with automated processing equipment
- Any business running internet-connected industrial equipment, even something as simple as a smart building thermostat connected to a BACnet controller
Small and medium-sized enterprises are especially vulnerable given little or no dedicated OT security teams. A 2024 scan showed more than 145,000 ICS devices were publicly available on the internet, including many protected by default passwords and lacking basic computer security solutions.
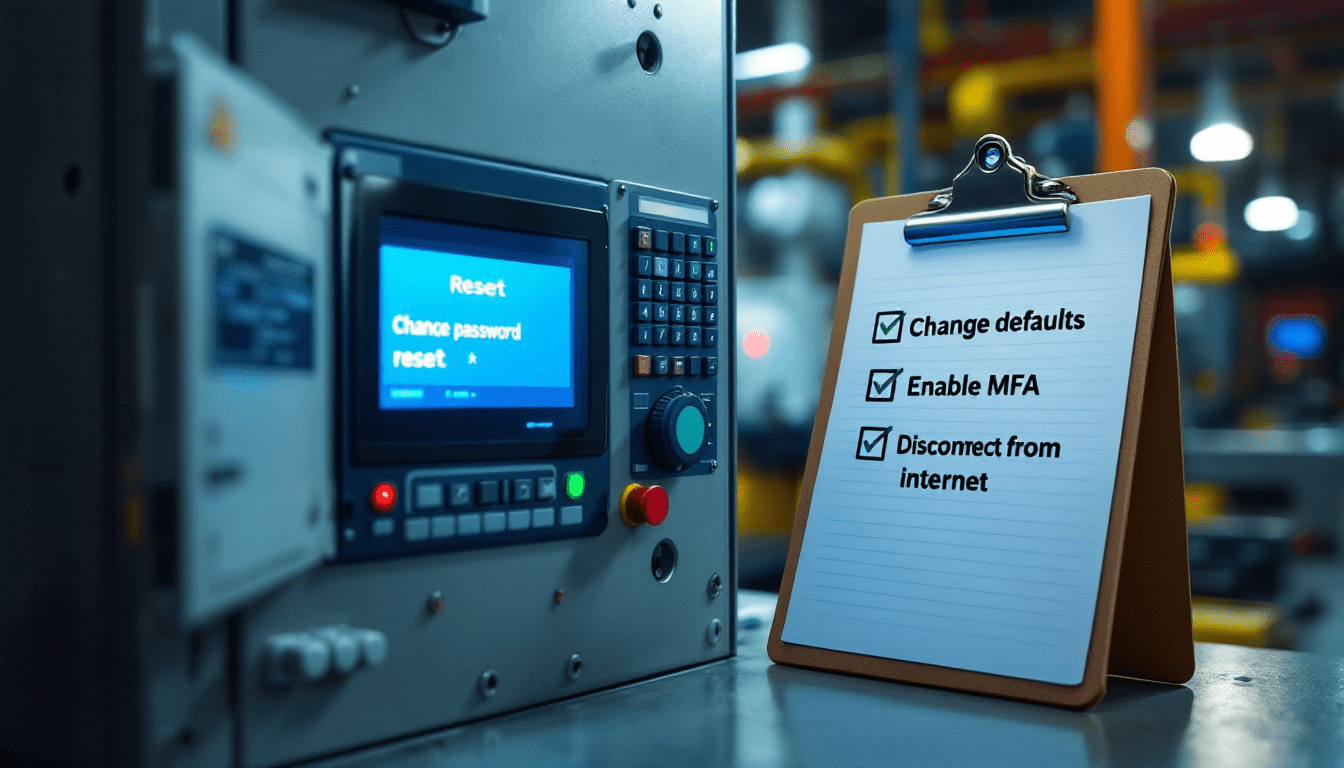
What You Can Do Right Now
The good news is that the most effective defenses against living-off-the-plant attacks are not complicated. They are just all too frequently overlooked.
- Change every default password in every PLC, HMI, SCADA system, and connected controller you use in your environment. The default from Unitronics was “1111.” The Norway dam was protected by a weak password on a public-facing interface. These are not advanced hacks.
- Disconnect OT devices from the public internet unless absolutely necessary. If remote access is necessary, install a VPN and firewall in front of it, with multi-factor authentication.
- Segment IT and OT networks. The Colonial Pipeline shutdown was not caused by ransomware on the pipeline itself but a case of the company losing trust in the separation between IT and OT and voluntarily cutting off operations. Proper segmentation prevents IT incidents from spilling over into OT.
- Inventory everything. You’re not going to be able to keep safe what you don’t know. Many organizations have PLCs and controllers installed years ago and forgotten about. Find them.
- Check OT network traffic for anomalies. The Norway dam attack remained undetected for 4 hours. Volt Typhoon spent nearly a year inside a utility in Massachusetts. Baseline what normal looks like and alert on abnormal activity.
- Back up PLC logic and configurations. If an attacker alters your ladder logic (as CyberAv3ngers did to Unitronics devices) you need to be able to quickly restore.
- Train your staff. Engineers and plant operators have to be able to recognize things that don’t look right, even when activity appears to come from a legitimate control interface.

How CinchOps Can Help
Living-off-the-plant attacks present a new category of threat that blurs the line between cybersecurity and physical safety. For Houston-area businesses, particularly in manufacturing, energy, and building management, the risk is both real and increasing. CinchOps has over 30 years of IT and cybersecurity experience helping small and mid-sized businesses build the type of protection that was once restricted to enterprises.
- OT and IT network assessment to discover exposed devices, default credentials, and segmentation gaps before attackers find them
- Network security architecture with proper segmentation of IT and OT environments using industry best practices
- Managed IT support with continuous monitoring that extends visibility to connected building systems and industrial equipment
- Cybersecurity planning and incident response so your team knows exactly what to do when things start to go wrong
- Remote access protection with properly configured VPN, firewall, and multi-factor authentication for any systems that must be accessible off-site
- Employee security awareness training tailored to your operational environment
Test your defenses before a “living-off-the-plant” attack does it for you. Get in touch with CinchOps today for a free consultation and find out where your OT security gaps are before someone else does.
Recommendations
Source Article: OT Attacks Get Scary With ‘Living-off-the-Plant’ Techniques – Dark Reading
Discover More:
- Dragos 2025 OT/ICS Cybersecurity Report
- IT vs. OT: Understanding the Difference
- Honeywell 2025 Cyber Threat Report
- CISA ICS Alert: Industrial Control Systems
- Forescout 2025 H1 Threat Review
![]()
FREE CYBERSECURITY ASSESSMENT