What the Q1 2026 Ransomware Numbers Mean for Houston Businesses
Construction Just Became A Top-Four Ransomware Target – A Plain-Language Read Of The Q1 2026 GuidePoint Ransomware Report
What the Q1 2026 Ransomware Numbers Mean for Cybersecurity Houston Businesses
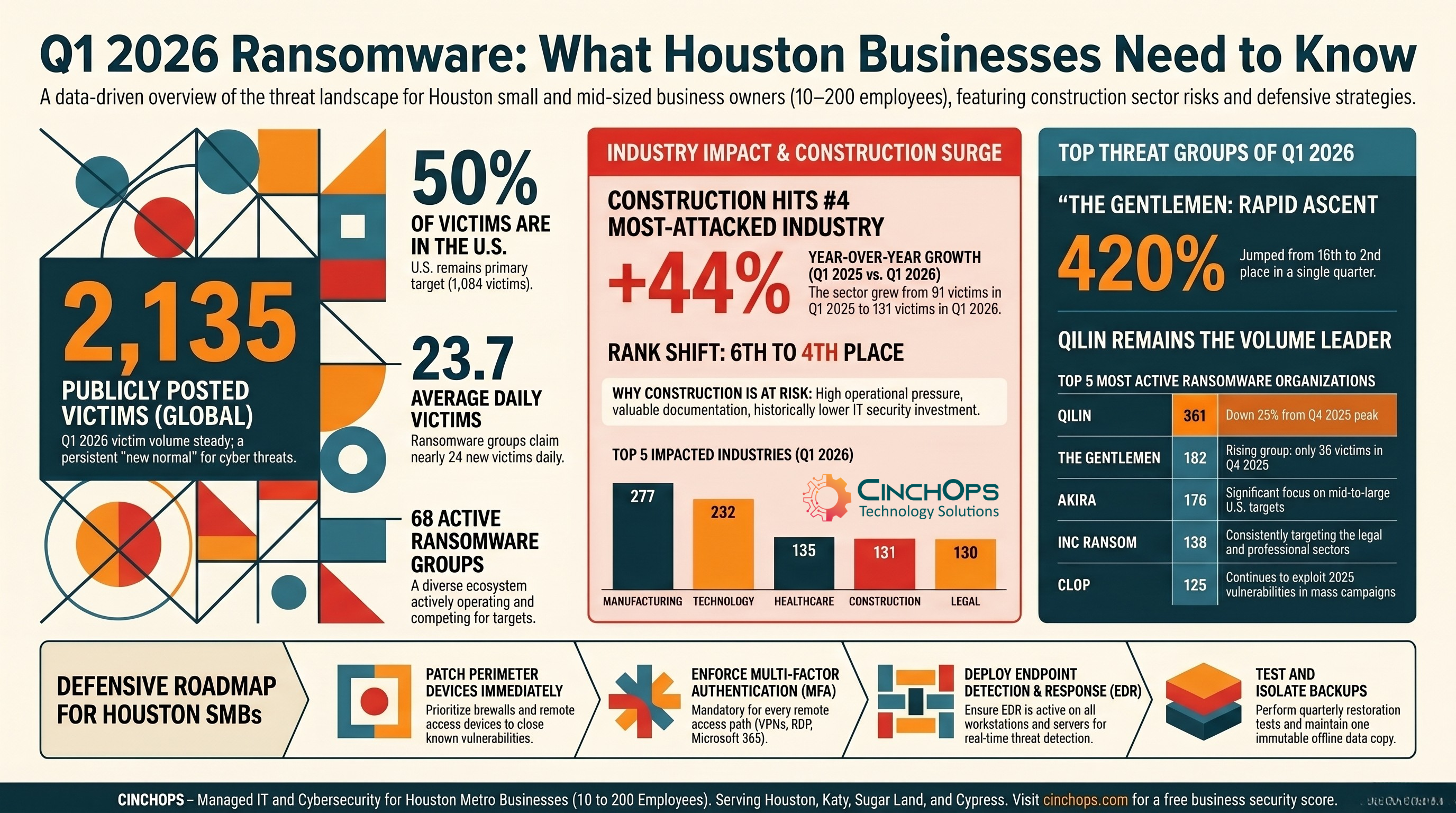
2,135 publicly posted victims. Construction up 44% year-over-year. Here's the read for Houston SMBs without the threat-intel jargon.
The first quarter of 2026 wasn't a record-breaker for ransomware. It was something arguably worse: steady. Researchers at GuidePoint Security's GRIT team logged 2,135 publicly posted victims between January and March, against 2,287 in Q4 2025 and 2,063 in Q1 2025. The volume hasn't moved much in over a year. That plateau is itself a story for cybersecurity Houston business owners who've been hoping the wave would crash on its own. It isn't going to.
Construction climbed from sixth place to fourth among the most-attacked industries, posting a 44% year-over-year jump in victim counts.
A new group called The Gentlemen vaulted from 16th to second place. Qilin and Akira lost some altitude, but mostly because their late-2025 Fortinet exploit windfall is closing. And Iran-aligned crews that mostly stayed regional in 2025 started reaching into U.S. soil with destructive wiper malware against companies like Stryker.
CinchOps is a managed IT services provider based in Katy, Texas, serving small and mid-sized businesses across the Houston metro area. CinchOps specializes in cybersecurity, network security, managed IT support, VoIP, and SD-WAN for businesses with 10 to 200 employees. We work with construction firms, CPA practices, law offices, and energy services companies across Houston, Katy, Sugar Land, Cypress, and The Woodlands, so when reports like this drop, we read them through a specific lens: which threats are likely to land at a Houston SMB, and what should the response look like by Monday morning?
What Changed in Q1 2026 (And What Didn't)
Headline numbers, the groups behind them, and the pattern shifts that matter for Houston cybersecurity planning.
The top-line stats look almost boring. 2,135 victims. 68 active groups. About 24 new posts per day. Compare that to the 2,287 victims in Q4 2025 and the 2,063 in Q1 2025, and the ecosystem is essentially holding pattern. GRIT attributes the slight QoQ dip to two things: Qilin and Akira coming off outlier Q4 performances tied to SonicWall SSLVPN exploitation, and the usual eastern-European Orthodox Christmas slowdown in early January.
What's underneath the average is more interesting. Qilin posted 361 victims, the most of any group, but down 25% from its Q4 peak of 484. Akira fell 22% to 176. The Gentlemen, a group that posted 35 victims in Q4 and ranked 16th, jumped to 182 victims and second place overall. That kind of operational tempo from a brand-new group almost always means experienced affiliates moved over from somewhere else, not that a fresh team learned the trade in 90 days.
Clop is also still draining the tank from its 2025 Oracle E-Business Suite mass-exploitation campaign. The group dumped 54 victims in a single day in early February. That's what mass-exploitation extortion looks like on a calendar: a long quiet ramp, then a dam break. If your business runs Oracle E-Business Suite and hasn't audited exposure since late 2025, that's a Tuesday morning conversation, not a Q3 budget item.
Geographically, the U.S. accounts for over half of all victims (1,084, or 50.77%). The U.K., Canada, France, Germany, and Italy fill out the next five spots. Thailand cracked the top 10 for the first time, which tracks with how ransomware operators expand into developing economies once Western targets get harder to hit. None of this is good news for cybersecurity Houston decision-makers. The U.S. share isn't shrinking.
The story isn't that ransomware is exploding. It's that 2,135 victims a quarter has become the new normal, and Houston SMBs are firmly inside that target pool. Steady-state ransomware is still a five-figure-per-day intrusion industry.
For context on how the most active groups stack up against each other, here's how GRIT's top five looked through Q1, with the changes that matter most for SMB defenders:
| Group | Q1 2026 Victims | QoQ Change | Primary Access Method | SMB Risk |
|---|---|---|---|---|
| Qilin | 361 | -25% | RaaS affiliates, broad targeting | High volume, less profitable per hit |
| The Gentlemen | 182 | +420% | Likely experienced affiliates | Top 3 across multiple industries |
| Akira | 176 | -22% | SonicWall SSLVPN flaws | Mid-to-large U.S. targets, including construction |
| INC Ransom | ~138 | Steady | Phishing, RDP, exposed services | Top group hitting legal sector |
| Clop | ~125 | Bursty | Oracle E-Business Suite mass exploit | Lagged 2025 campaign still claiming victims |
Why Construction Is Suddenly a Top-Four Target
131 victims. Up 12% QoQ. Up 44% YoY. The Houston metro has a lot of construction firms, and ransomware crews have figured out why they're worth hitting.
Manufacturing has been the most-attacked industry for over a year. That hasn't changed. What changed is construction moved from sixth to fourth, with 131 publicly posted victims in Q1, up from 117 in Q4 and 91 in Q1 2025. It's one of the few sectors that grew while the overall ecosystem stayed flat. Twenty-two distinct ransomware groups claimed construction victims last quarter, with Qilin, Play, Akira, and DragonForce accounting for 55% of them.
Why now? GRIT's analysis lines up with what we see in the field across construction IT engagements. The sector has a target profile that ransomware crews specifically look for: operational pressure that drives ransom payments, project documentation that carries independent extortion value, and infrastructure that's typically been treated as a cost center rather than a business risk.
Halt a construction firm's project management system in week three of a 16-week build, and you don't just lose access to files. You lose the schedule, the bid documents, the change orders, the RFIs, and the connection to half a dozen subcontractors and one general contractor whose networks you're now potentially exposing. The pressure to pay ransoms in this sector is structural, not technical.
The other half of the equation is what doesn't exist at most mid-sized contractors. Limited regulatory pressure, no dedicated security personnel, often no EDR on field laptops, consumer-grade VPN on the trailer router, and patching schedules that revolve around whoever has time on Friday afternoon. Compare that to a healthcare practice with HIPAA, a CPA firm with FTC Safeguards, or a wealth manager with SEC requirements, and the maturity gap is obvious. Ransomware crews see it too.
"Houston construction companies might think they're too small to target. The 131 victims in Q1 say different. The crews aren't picking by headcount or revenue, they're picking by which doors are unlocked, and most of the doors I see in this sector are wide open."
One Q1 victim's leaked data explicitly referenced federal defense project work. That's a mid-sized contractor's compromise turning into a national-security-adjacent incident. For Houston firms working on energy infrastructure, port projects, federal building maintenance, or anything with a state or municipal tie, the same dynamic applies. The contract you didn't think had cyber exposure probably does.
Most ransomware victims had basic gaps a 30-minute review would have found
If you haven't audited your remote access, EDR coverage, and backup integrity in the last six months, you're operating on faith. We can walk through it with you.
Talk to CinchOpsQilin Still Leads. The Gentlemen Came Out of Nowhere.
Two very different operating models, both worth understanding.
Qilin runs an open-recruitment Ransomware-as-a-Service model. That structure is what gets them to 361 victims in 90 days. It's also what costs them on the back end: GRIT notes Qilin has higher non-payment rates than competitors like Akira, because their affiliates aren't all skilled negotiators and their targets aren't always able to pay. Volume is the strategy. Profit per victim is not.
The Gentlemen are the opposite story. Thirty-five victims in Q4 2025. 182 in Q1 2026. That kind of jump doesn't happen because a new team got better at hacking in three months. It happens because experienced affiliates rebranded after their old shop got disrupted, retired, or became unprofitable. The targeting and tradecraft for The Gentlemen looked mature from day one. Their top three sectors include manufacturing, technology, and construction, which is exactly the spread that suggests recycled affiliates with established attack playbooks.
176
361
182
138
125
For Houston SMBs, the practical implication is straightforward. Group names are a marketing layer. The same affiliates often work for multiple brands, sometimes simultaneously, and rebrand whenever law enforcement attention or internal drama makes the old name a liability.
That means defensive resources are better spent on the techniques (phishing-resistant MFA, patched perimeter devices, EDR with behavioral detection, tested backups) than on tracking which group is "trending" this quarter.
This is also why the Q1 announcement that Scattered LAPSUS$ Hunters was "retiring" between August and October 2025 should be filed under "watch what they do, not what they say." ALPHV/BlackCat, DarkSide, REvil, and Conti all announced retirements before either rebranding or coming back. The infrastructure, the tools, and the affiliates persist. The names just get repainted.
NightSpire, Fortinet, and the Patch You Probably Forgot
A relatively new group with 175 victims, hitting through a year-old vulnerability that thousands of businesses still haven't patched.
NightSpire is one of the more aggressive newer ransomware operations, posting 74 victims on its data leak site in Q1 2026 alone. Over 40% of their victims are in the United States.
Manufacturing, technology, and construction are their top sectors, which is the same target profile that tends to land in Houston. What makes NightSpire worth paying attention to isn't sophistication. It's the access vector.
NightSpire's primary entry point is CVE-2024-55591, an authentication bypass in FortiOS and FortiProxy that lets an unauthenticated attacker get super-admin privileges on the device. Fortinet disclosed it on January 14, 2025. Hundreds of thousands of internet-facing Fortinet devices were exposed at disclosure. A meaningful share haven't been patched 13 months later. NightSpire is one of several groups walking through that door.
If your business runs a Fortinet firewall, FortiProxy, or any FortiGate appliance with web admin exposed to the internet, this is a check-it-this-week task, not a quarterly review item. Secondary access vectors NightSpire uses are RDP brute force and phishing campaigns. Once they're in, they move laterally with PowerShell, PsExec, and WMI, then exfiltrate data through MEGA before posting victims to their leak site.
- Patch CVE-2024-55591: Confirm your Fortinet appliances are running a fixed version. Don't assume your IT provider did it.
- Restrict Admin Access: Web admin interfaces on perimeter devices should be on a management VLAN, not the internet.
- Require MFA Everywhere: Every remote service. SSL VPN, RDP, admin portals, no exceptions.
- Deploy EDR Across All Endpoints: Workstations and servers. NightSpire's lateral movement uses tools (PowerShell, PsExec) that EDR can flag in real time.
- Restrict RMM Tools: AnyDesk, Chrome Remote Desktop, and similar utilities should be allowlisted, not "available."
Iran-Aligned Wipers Are Now Hitting U.S. Soil
The Stryker attack in March 2026 changed the calculation. Wipers don't ask for a ransom.
For most of 2025, Iran-aligned cyber operations stayed regionally focused. That changed after the February 28, 2026, U.S. and Israeli strikes on Iran. The Handala Hack Team, a hacktivist persona with assessed ties to Iran's Ministry of Intelligence and Security, claimed responsibility for a destructive malware attack against Stryker, a Michigan-based medical technology firm, on March 11, 2026. The attack reportedly disabled tens of thousands of systems.
The distinction that matters here is wipers versus ransomware. Ransomware encrypts your data and offers a (terrible, but possible) payment path to recover it. Wipers destroy with no recovery option. Backups are the only path out. Handala has deployed several wiper variants (Coolwipe, Chillwipe, Bibiwiper) all designed to maximize disruption rather than collect a ransom.
Most cybersecurity Houston SMBs are not Stryker. The threat profile from these operations is opportunistic, not targeted. Iran-aligned crews look for accessible vulnerabilities and weak credentials, then pick a justification afterward (a 2019 acquisition of an Israeli company, U.S. headquarters, defense industry adjacency). The defensive playbook against opportunistic targeting is the same playbook against ransomware, with one upgrade: backup integrity becomes existential.
If your only backup is a Veeam repository sitting on the same network as your production servers, a wiper takes both. If your backups are in a separate, immutable cloud target with credentials that aren't stored on workstations, you have a recovery path. The principle is the same one that's been on the recommendation list for ransomware for five years. The consequence of getting it wrong is just less forgiving.
The AI Supply-Chain Risk Is No Longer Theoretical
In February 2026, an attacker published 314 malicious skills to an agentic AI platform's marketplace. Real malware. Real victims.
This one is the leading indicator nobody asked for. VirusTotal documented the first confirmed large-scale supply chain attack against an agentic AI platform in February 2026. A threat actor uploaded 314 malicious skills to OpenClaw's ClawHub marketplace, disguised as benign tools like "Yahoo Finance" and "Crypto Analytics." The skills themselves contained no malware. The malicious behavior was emergent: the skills instructed the AI agent to download and execute external payloads as part of a "setup procedure," and trusted users following trusted AI agent instructions ended up running info-stealers on their own machines.
The attack worked because traditional malware detection looks for code signatures. The skill files didn't have any. The threat lived in the workflow, in the human acting as interpreter between benign-sounding instructions and a malicious command line.
For Houston SMBs adopting AI tools, copilots, or agentic platforms, this isn't a "down the road" concern anymore. It's a Q2 governance conversation. The fundamentals: where can the AI agent execute code? What can it read or send? Who reviews extension and skill installs? Is there an audit log? Most companies adopting AI agents this year have answered exactly none of those questions, which is why this is going to keep happening.
How CinchOps Helps Houston Businesses Stay Off the 2026 Victim List
The Q1 2026 report doesn't reveal a single new attack technique that fundamentally changes defensive priorities. It confirms that the same controls that worked in 2024 still work, and that the businesses paying ransoms in 2026 mostly skipped them. That's the lane CinchOps operates in: getting the unglamorous fundamentals deployed, monitored, and verified for Houston SMBs that don't have a dedicated security team.
- Patch Management That Actually Closes The Gap. Fortinet, SonicWall, Cisco, Microsoft, and the rest of the perimeter stack get patched on a defined cadence with verification, not "when we get to it."
- EDR Deployment And Tuning. Every workstation and server runs endpoint detection that catches lateral movement tools (PowerShell abuse, PsExec, WMI) before they become an incident.
- MFA On Every Remote Access Path. SSL VPN, RDP, Microsoft 365, third-party SaaS. Phishing-resistant where possible (FIDO2, Windows Hello).
- Backup Architecture That Survives A Wiper. Immutable cloud targets, separated credentials, regular restoration testing. Not just "we have backups."
- Vendor and Supply-Chain Hygiene. Subcontractor access reviews, scoped VPN tunnels, conditional access for third-party users. The construction sector's Q1 numbers say this is overdue.
- Local Houston Response. When something does happen, you have a team in Katy with hands on your environment, not a ticket queue in another time zone.
The 2,135 victims in Q1 weren't all sophisticated attacks. Most were access vectors that should have been closed years ago. CinchOps closes them.
FAQ: Q1 2026 Ransomware and Cybersecurity Houston
Is ransomware getting worse for cybersecurity Houston businesses in 2026?
Ransomware activity is steady, not exploding. GRIT tracked 2,135 victims in Q1 2026, slightly below Q4 2025 and slightly above Q1 2025. The threat to Houston SMBs hasn't grown dramatically, but it hasn't receded either. The volume that worried you in 2024 is the new normal, and the U.S. accounts for over half of all victims globally.
Why is construction suddenly a top ransomware target?
Construction posted 131 victims in Q1 2026, up 44% year-over-year and rising from sixth to fourth place. The sector combines high operational pressure to pay ransoms, valuable project documentation, connectivity to client networks, and historically thin cybersecurity investment. Ransomware groups have figured out that mid-sized contractors are profitable targets with weak defenses.
What is CVE-2024-55591 and why does it matter for Houston businesses?
CVE-2024-55591 is a critical authentication bypass in Fortinet FortiOS and FortiProxy that lets attackers gain super-admin access without credentials. NightSpire and other ransomware groups are actively exploiting it. Any Houston business running Fortinet appliances should verify the patch is applied, since hundreds of thousands of devices remain exposed over a year after disclosure.
What's the difference between ransomware and a wiper attack?
Ransomware encrypts your data and demands payment for decryption keys. Wipers destroy data with no recovery option except restoration from backups. Iran-aligned groups like Handala have deployed wipers (Coolwipe, Chillwipe, Bibiwiper) against U.S. companies in 2026. For Houston SMBs, this means backup integrity moves from important to existential.
What should a Houston SMB do this week based on the Q1 2026 report?
Three things. First, confirm Fortinet appliances are patched against CVE-2024-55591. Second, verify every remote access path requires MFA, including third-party vendors. Third, run a backup restoration test if you haven't in 90 days. These three steps would have prevented a meaningful share of the 2,135 ransomware incidents tracked in Q1 2026.
Discover More
Resources
Sources
- GuidePoint Security GRIT Q1 2026 Ransomware and Cyber Threat Insights report - 2,135 publicly posted ransomware victims, 68 active groups, industry and group breakdowns
- Fortinet PSIRT advisory on CVE-2024-55591 - authentication bypass affecting FortiOS and FortiProxy disclosed January 14, 2025
- CISA cybersecurity advisories on Iran-aligned threat activity and ransomware operations
- VirusTotal February 2026 reporting on the OpenClaw ClawHub malicious skills campaign affecting agentic AI supply chains